The modern cybersecurity model is based on four pillars: vendor trust, delineation, data hiding, and updates. By purchasing a device with a pre-installed operating system, the user votes with his own money for trust in the manufacturer. Delimitation and data hiding are integrated into the architecture of modern operating systems, but here's how to organize the update of the operating system itself? It cannot update itself, it needs both additional applications that download and install updates, and the server side on the manufacturer's side. And this is an additional cost for the company that produces the operating system. At the same time, any commercial activity implies minimizing costs and maximizing income. At the same time, maximizing income, as well as minimizing costs, can lead to extremely unpleasant consequences for end users of devices.
Malicious software
Malicious software integrated into smartphone firmware is one of the good ways to make extra money from users. You can even lower the price of the smartphone itself by increasing the revenue side through advertising that cannot be turned off. Or selling personal data of smartphone users to other companies that specialize in their processing. At the same time, it is rather difficult to detect the presence of malicious software bugs in the firmware, unless they clearly manifest themselves. The manufacturing company can always say that it was a diagnostic module that they forgot to disable 'by mistake'. Maybe it's true, or maybe not, none of us can verify this. And OnePlus, when it was caught collecting user data, explained this by the need for “better post-sales preparation”, and it was possible to refuse to collect statistics only through a well-hidden item in the settings menu.
Also, builders of homemade firmwares sin by integrating malicious software into the operating system of smartphones. But this is also quite understandable: you want to make money on your work, but users are in no hurry to pay. And collecting donations, too, somehow does not pay off the time spent. And advertisers pay for every thousand impressions of an advertising banner …

Not very conscientious smartphone dealers also strive to install malicious modules on a smartphone in order not only to make money on the sale of the device itself, but also to get additional income: the time spent is minimal, the profit is maximum. So, by buying a smartphone on a dubious site on 'Aliexpress', you risk getting an unpleasant addition to the functionality of your gadget. And not only on Chinese marketplaces you run the risk of buying a smartphone with preinstalled malicious modules: in March 2017, Check Point revealed malicious software running on smartphones from manufacturers known in a wide range of users. Moreover, the source of the infection remained unknown.
The most annoying thing is that it is almost impossible to remove the malicious software integrated into the smartphone's firmware without root rights. Even if the antivirus scans your device and finds files containing malicious functionality, it will not be able to delete them. And getting root-rights is a rather time-consuming process and without guarantees of success, and even without studying information saturated with technical terms from w3bsit3-dns.com forums, it is practically impossible.
Malicious updates
The operating system software update system implies, as I have already mentioned, not only additional modules on the side of the smartphone itself, but also a server binding, which gives new firmware images. It costs money to create and maintain it all in working order, which you want to save. And here companies come to the aid of third-tier manufacturers that provide services for distributing firmware updates for smartphones. But these companies also want to make more money on their services, or people in uniform sewn onto civilian shirts may come to them. In 2016, the World Wide Web was stirred up by a scandal over a smartphone firmware update program. The application, positioned as a firmware update tool manufactured by Shanghai Adups Technology Company, collected and sent confidential data collected from users' smartphones to the company's servers. So the process, which is designed to improve the security of devices, led to their compromise. The desire of smartphone manufacturers to reduce the cost of distributing updates has come to their side.
It is also possible to compromise the smartphone's firmware at the level of its transmission over the network. If the image is downloaded via an unsecured cryptographic channel or there is no check for the integrity of the downloaded file, then the attackers do not need anything, having compromised the server or the communication channel, and install additional malicious modules directly inside the firmware.

Errors in the operating system
It would be a mistake to believe that since the update system for smartphones may not be well protected or, even worse, infected with malware, then it should not be used. It is necessary, and I myself consider the time of software support for smartphones as one of the main parameters by which I choose a manufacturer. Unfortunately, the reality is that we all make mistakes, and software developers also make mistakes in the process of creating their software products. Considering that the operating system, device drivers, system applications are complex software, errors in its development are inevitable. Some of these errors can be used by cybercriminals to penetrate your smartphone or to gain higher rights on the device. Firmware updates allow you to proactively protect yourself from these kinds of threats, leaving attackers with nothing. At the same time, there is a risk that in the process of fixing errors, the manufacturer may break some important function. And not only from third-tier manufacturers, but also from large vendors. For example, after one of the recent OnePlus updates, the camera stopped working for some users. This cup did not pass and Apple – after receiving the update to iOS version 11.2, the function of unlocking the smartphone by face, FaceID stopped working for many users. It has happened, is and will happen to every software vendor. But those who have properly built software quality assurance processes will have less such embarrassment.
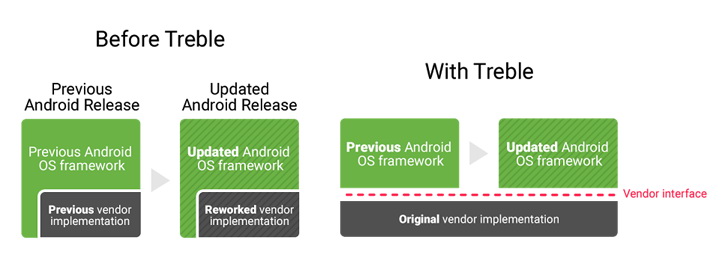
In order to improve the update process Android, Google has divided the operating system into two parts: the kernel and the user interface, and the kernel can be updated independently of the front-end. Google called it 'Project Treble'. Now the manufacturing company, starting with version Android 8.0, has the ability to hand over updates to the operating system kernel in the hands of Google, and it itself only deals with a custom shell, errors in which do not greatly affect the overall security of devices. This will certainly improve the stability of smartphone firmware updates as well as enhance the overall security of the entire ecosystem Android.
Conclusion
If you buy a smartphone with an unofficial firmware installed from dealers with an incomprehensible reputation, then you run the risk that your confidential information will be in the wrong hands. In addition, colorful Chinese language advertisements may be constantly displayed on the smartphone screen, which does not increase the battery life of the smartphone. And getting rid of all this miracle without root rights will be almost impossible: no antivirus application will help.
And even if you bought a smart device from a reliable seller and with an official firmware, the manufacturer himself, in pursuit of a penny saving, can put a pig on you.
The most reliable option from a security point of view is buying a smartphone from a large, well-known manufacturer, on which the official firmware is installed. In the case of Android, it is also desirable that it be an operating system with Treble support. In this case, the probability of encountering malicious modules in the firmware is minimal. Keep your devices in good health!
Ilya Rabinovich
