Antivirus company ESET has announced that it has detected an ongoing malicious cyberattack in the Google Play app store, affecting millions of users Android.
It is noted that a total of 42 applications were detected that relate to this campaign to distribute unwanted adware; half of them were still available at the time of discovery. The security team at Google removed these apps after company notification, but they are still available in third-party stores.
These applications provide the promised capabilities – simple games, online radio, video downloads – but also act as adware, with common functionality. In total, these malicious applications have been downloaded 8 million times in the last year.
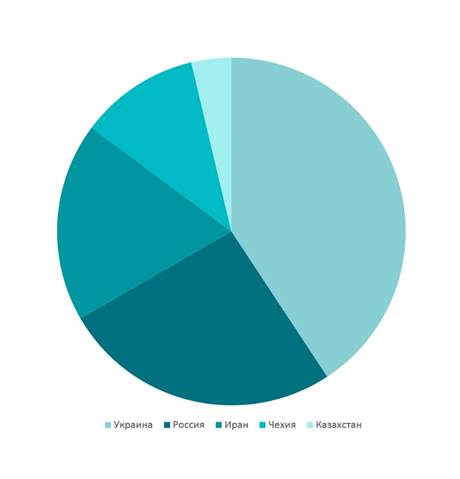
Top 5 countries affected by the Ashas family
Apps use various tricks to get onto victims' devices and go unnoticed: for example, they don't show ads until the device is unlocked. If the user tries to find out which application triggers the ad display, the program will impersonate Facebook or Google.
Also interesting is how the Ashas family hides their code under the com.google.xxx library name.
While analyzing the applications, ESET experts noticed that the creator of the malware left many traces. Researchers tracked the developer using open source information. He turned out to be the campaign operator and the owner of the C&C server.
